Share this
How to Get Ransomware Protection: Best Security Tips and Tricks
by Robert McNicholas on August 22, 2019
Ransomware - What Is It & How To Remove It
 One of the biggest threats your business or organization can face is ransomware. Most business owners are aware of malware and spyware but probably have not come across ransomware. Ransomware is a form of malware but it's different from malware in its approach. Malware aims to try to lead you to offers and affiliate promotions to generate profits while spyware collects your data or tries to get access to sensitive financial accounts.
One of the biggest threats your business or organization can face is ransomware. Most business owners are aware of malware and spyware but probably have not come across ransomware. Ransomware is a form of malware but it's different from malware in its approach. Malware aims to try to lead you to offers and affiliate promotions to generate profits while spyware collects your data or tries to get access to sensitive financial accounts.
Ransomware is different in that it prevents access to your valuable files. It will lock up certain folders, hide your files, or even lock up your whole hard drive. The ransomware created by hackers will then demand a ransom in return for access to your files (hence the name). The worst part is that you don't even know that you'll regain access to your files even if the ransom is paid. In fact, they may demand even more money or lock up everything again after giving you back access for a short period of time.
As you can imagine, this can cause chaos and even stop your business from running. It is also scary knowing that somebody else may have access to sensitive data and important functions for your business. Ransomware prevention starts with knowing how it can infect your network and implementing the right ransomware prevention strategies.
How Do You Get Infected with Ransomware?
The most common source of ransomware attacks originate with phishing attempts via email. Emails pretending to be people, companies and organizations you're familiar with may tell instruct you to download an attachment file. In other cases, users may have set their email functions to automatically download attachments. This makes it easy for the hacker to quickly gain access to your system.
Of course, ransomware can also be downloaded when users visit bad neighborhood sites. They may even be bundled with software programs that looks like they are safe from the outside. Prevention of ransomware starts with knowing how users are typically exploited. This information will allow you to train your employees and team members so that they are extra cautious about how they interact with the Internet.
Signs that You've Been Hit with Ransomware
How do you know if you've been hit with ransomware in the first place? Other than the actual ransom itself, there are some early signs that will give it away. Here's a quick list of the clues you should look for:
- Certain files and folders get blocked from being opened. There have been no changes to the permission settings for them recently.
- You are not able to open your firewalls, antivirus programs, anti malware programs, or other solutions that can help detect and fix potential problems.
- You can still access certain functions of the computer. However, the functions are severely limited in terms of what you're able to do. The goal of the hacker here is to start making you feel desperate.
- You may see some of your files and folders start disappearing out of nowhere. It could be a possibility that the ransomware is in the process of encrypting your data.
- You start witnessing a severe slowdown of your computer for no reason. Opening the start task manager may reveal that there are certain programs that are running that you do not recognize.
- If you wait long enough, you'll be sent a ransom that you are instructed to pay in order to restore your computer.
10 Tips for Ransomware Prevention
Preventing ransomware requires that you cover all your bases. First, you want to prevent it from happening. Next, you want to be able to detect attacks so that you can respond quickly. Finally, you want to be able fix the ransomware infection in the worst case scenario. To give you some guidance, here's a list of 10 tips to prevent ransomware:
Tip #1: Always Back Up Your Data
 The most important thing you can do is to back up your data. Make sure it is backed up to an external hard drive or server that's not connected to your network. You do not want the ransomware to connect to a backup hard drive that's connected to your main hard drive. You will also need to back up on a regular basis as waiting weeks between back ups means a lot of lost data if you have to wipe your old system.
The most important thing you can do is to back up your data. Make sure it is backed up to an external hard drive or server that's not connected to your network. You do not want the ransomware to connect to a backup hard drive that's connected to your main hard drive. You will also need to back up on a regular basis as waiting weeks between back ups means a lot of lost data if you have to wipe your old system.
Alternatively, you can choose to back up and host your file on cloud services. Since your data is not being hosted on your system, you can easily wipe your system and simply get your data back from your host. If you go with this option, make sure you choose a hosting provider that is reputable, offers excellent customer support, and takes security seriously.
Tip #2: Establish Ransomware Prevention Education and Policy
A big part of keeping your network safe is to establish clear protocols. For example, you should not allow employees to set up automatic downloads of email attachments or allow installation of apps that are not approved by you. Educating employees and team members about how to interact with the Internet will also play a large role in ransomware protection.
You want to teach employees and team members how ransomware infects networks. There are many tricks hackers use such as naming files like "report.doc.exe" to make users think that it's a document file. Phishing attempts are also very tricky too as hackers send emails that make it look like it's coming from well-known companies like Chase and Paypal.
In some cases, protocols need to be reinforced through system restrictions. For example, blocking untrusted sites and preventing file downloads from entering the network are two easy solutions that can be implemented on your network. By setting these restrictions, you won't have to worry about users accidentally bringing in ransomware into your system.
Tip #3: Install the Right Security Software
You probably already have an antivirus software in place. However, the best ransomware prevention will probably be a malware software dedicated to protect you from malware, spyware and ransomware. In many tests, these anti malware programs have found and blocked many types of malware that antivirus programs haven't been able to detect. Think of it of having another layer of security.

Strong ransomware prevention software programs also protect your network in real time. If the program detects that a risky file was added or is attempting to be downloaded, it will quarantine or block it right away. For optimal ransomware prevention, you need to have a way to respond to the file once you interact with it. Prevention alone is not enough to deter infection.
If you still end up getting infected, many of these programs can help in removing it from your system. However, some ransomware can be very complex. They'll close the programs you're running and block antivirus and anti malware programs from running. So while these programs are usually effective, they cannot offer you full ransomware prevention. To increase the effectiveness of these programs, update the virus and malware definitions regularly.
Tip #4: Set Up Multi-Tier Network Access
Instead of allowing your network to be accessed from one entry point, you want to create levels of security. This means that only certain users are allowed to access the most important parts of your network. So if the ransomware manages to get inside your system, it won't be able to take over and hold your entire system hostage.
You can set up passwords and two-factor authorization to allow entry into the important parts of your network. This is an effective way of defending against ransomware because the ransomware will be limited in what it can do to your system. You can even separate your network into multiple parts if you want even greater security.
Tip #5: Set Up a Firewall
A firewall is a classic antivirus solution that can also be effective for ransomware prevention. A firewall will block unauthorized access to your network. Sometimes it will help to set up multiple firewalls. Windows has its own firewall that many people use. But it can also help to have more two, even three firewalls set up for your network.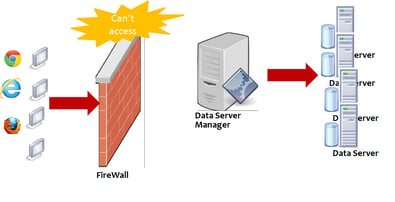
Many antivirus solutions come with their own firewall programs, so they can offer additional protection beyond your Windows firewall if it fails to prevent ransomware from coming in. The only problem with using multiple firewalls is that some of them can conflict with each other. Many developers will point out conflicts about their antivirus and firewall solutions, so make sure you read up on them.
Tip #6: Create a Security Schedule
Just because you've installed an antivirus and anti malware program doesn't mean that you aren't infected. There may still be ransomware in your system just waiting to be executed the moment it finds a good opportunity to do so. That's why your ransomware prevention strategy should include a regular schedule of scanning and updating the definitions.
There are always new types of viruses and malware being created on a daily basis. It's possible that you may even have one in your system that hasn't been detected by your programs. When you update and scan regularly, you'll be able to identify new problems that the software programs may have missed previously. You can't make assumptions when it comes to taking proper ransomware prevention measures.
Tip #7: Keep Your System and Apps Updated
There is a reason why software developers continue updating their products. There are exploits that may have gone undetected, new ways for hackers to access your network, and vulnerabilities that need to be fixed. As a result, you should take your updates very seriously. The list of things include your operating system, common web apps (browsers, Flash, Java, etc.), and third party applications.
This can be very tedious for some businesses and organizations because they may not like working with a new version of the operating system. However, it's not something that should be taken lightly as hackers are always working to target vulnerabilities. If you do want to stay on the same version, make sure you read the developer patch notes carefully to see what the updates were for. You can sometimes find individual upgrades that address the vulnerability but do not make other changes.
Tip #8: Work on the Most Vulnerable Points
Adding improvements and fixes to the most vulnerable points will go a long way for ransomware prevention. There are many things you can do such as disabling file sharing so that the infected file does not get spread. You can also shut off vulnerable wireless connections like Bluetooth. You can even disable autoplay so that USB sticks, DVDs, and connected mobile devices won't run the ransomware when plugged in.
Then there are the browsers and apps. You want to disable automatic downloads, block pop-ups, and prevent scripts from running on your browsers. If you run your own email server, you can block unknown email addresses, optimize your spam filters, only allow signed files to be downloaded, and allow attachments to be downloaded into quarantined folders.
Tip #9: Block Access from Unknown IP Addresses
Hackers often control the ransomware from an outside location once you are infected. To minimize the control they have over your computer and system, you can create a whitelist of IP addresses and block access from unknown IP addresses. This might not prevent the ransomware from affecting your system. However, it can help deter some of the damage it can cause.
Tip #10: Prepare for the Worst Case Scenario
It helps to prepare for a rainy day. If you get infected with ransomware, you want to make sure that your business or organization is able to continue running. That's why you want to have the right business continuity strategies in place beforehand. Don't wait until you are infected to figure out what to do.
As mentioned earlier, a big part of prevention is to make sure you back up your data on a regular basis. You want to take that data and try to get your business back up and running. A simple solution for doing this is to find a cloud hosting company that you trust. While you are in the middle of wiping your previous system, you'll still be able to generate revenue for your business.
What to Do If You Still Get Hit with Ransomware
If you've done everything you can and you still ended up getting infected, there are still some things you can do. The first thing you want to do is quickly cut off Internet access to the afflicted computer. Then follow up by disconnecting it from the network if you haven't set the proper settings already. You want to isolate the infected computer so that it doesn't spread throughout your network.
Finally, shut off the computer as quickly as possible. As a matter of fact, it might be smarter to do this right away and cut off the computer's connection with the network. Sometimes the ransomware needs time for it to start changing your system. If you shut the computer off right away, it doesn't get that critical time to execute its program.
Can You Recover from a Ransomware Infection?
Yes, it is definitely possible to recover from a ransomware infection. Sometimes doing a simple system restore may take the computer back to the point before the ransomware was installed. But of course, the ransomware may have locked you out of the system or blocked certain functionalities. In this case, you may want to wipe the system and install everything with your back ups.
 As mentioned earlier, you should not pay the ransom. There are cases where the hacker will give back access after you have paid but there is no guarantee. You don't know if the hacker will ask for another payment after the first or if the payment will only provide access to a limited number of files. Even if the hacker honors the first payment, how do you know if the hacker won't come back again to do the same thing?
As mentioned earlier, you should not pay the ransom. There are cases where the hacker will give back access after you have paid but there is no guarantee. You don't know if the hacker will ask for another payment after the first or if the payment will only provide access to a limited number of files. Even if the hacker honors the first payment, how do you know if the hacker won't come back again to do the same thing?
If you absolutely need to recover the computer or your network has been severely affected, you need the help of professionals. You want to start by getting another set of workstations and servers up to continue running your business. Then you'll want to hire professionals that offer a disaster recovery service. It's possible to recover the computer and network, but it can take a lot of time to do so.
Overall, making sure you work with a reputable security company to protect your network is more critical than anything else. Don't wait until your network gets attacked by hackers. You need to be proactive about security to protect your revenue, customer data, employee data, and sensitive business information. Techspert Services has helped many businesses and organizations protect their networks from viruses, malware, spyware, ransomware, and more.
Give us a call today to learn what we can do for you. We'll get straight to the point and give you a fair quote for our Ransomware prevention services.
Share this
- Featured (119)
- Best Practices (76)
- Business (67)
- Small Business (67)
- Security (38)
- Managed Services (29)
- Business Growth (27)
- Technology News (26)
- Google For Work (22)
- it support (15)
- Social Media (13)
- Technology (11)
- Malware (10)
- Google (9)
- News (9)
- Cloud (6)
- seo (6)
- Backup Storage (5)
- Website (5)
- Communication (4)
- Productivity (4)
- Ransomware (4)
- Research (4)
- Analytics (3)
- Technology Support (3)
- Windows (2)
- anti malware (2)
- email (2)
- how to (2)
- laptops (2)
- mobile (2)
- Hubspot (1)
- data recovery (1)
- twitter (1)
- April 2024 (2)
- March 2024 (2)
- November 2022 (3)
- October 2022 (1)
- September 2022 (3)
- August 2022 (3)
- December 2021 (3)
- November 2021 (3)
- October 2021 (1)
- September 2021 (3)
- August 2021 (3)
- July 2021 (1)
- March 2021 (1)
- February 2021 (7)
- January 2021 (1)
- March 2020 (1)
- August 2019 (1)
- April 2019 (4)
- March 2019 (6)
- December 2018 (10)
- November 2018 (10)
- August 2018 (1)
- July 2018 (9)
- June 2018 (4)
- May 2018 (4)
- October 2017 (3)
- September 2017 (6)
- August 2017 (6)
- July 2017 (12)
- June 2017 (12)
- May 2017 (3)
- March 2017 (5)
- February 2017 (2)
- August 2016 (2)
- June 2016 (4)
- January 2016 (1)
- December 2015 (3)
- November 2015 (3)
- October 2015 (3)
- September 2015 (3)
- August 2015 (2)
- July 2015 (4)
- June 2015 (3)
- May 2015 (2)
- April 2015 (1)
- March 2015 (1)
- February 2015 (1)
- January 2015 (2)
- November 2014 (4)
- October 2014 (11)
- September 2014 (5)
- August 2014 (6)
- July 2014 (7)
- June 2014 (8)
- May 2014 (3)
- April 2014 (3)
- March 2014 (2)

